Authentication and Authorization has been part and parcel of almost every application software that is built. And as a developer, we spend lot of time and effort in incorporating these two in every application we built. While I would like to leave the Authorization for another post for some other day in the future, I thought I would share some thoughts on the Authentication.
Typical setup looks like this…
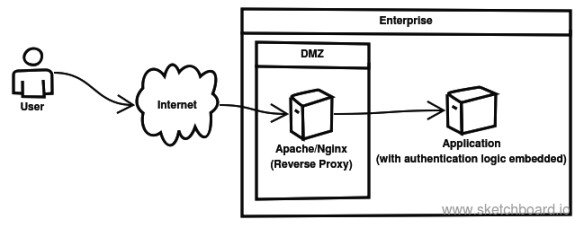
While hand coding the Authentication gives the developer full control, there are so many problems with this…
- Obviously we end up re-inventing the wheel every time
- Security aspect is always taken for granted
- Support for various authentication approaches and multi factor authentication requirements would soon call for a lot of additional effort to cater to the business.
Thanks to so many authentication solutions available as commodity in today’s world, most of the application developers simply integrate their application code with the authentication solution that has been chosen. This is certainly a good thing, since now the major responsibility around security aspects is pushed out of your application boundary.
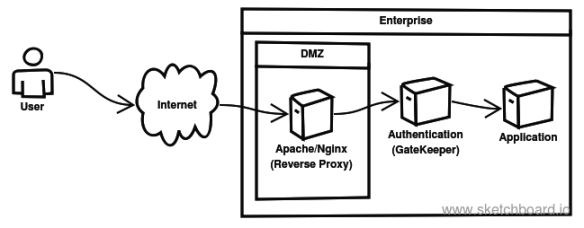
In the above setup, we see that our application is becoming responsible for making the decision asserting whether the user is authenticated or not. As we all know, authentication is a favourite target for attackers to exploit and get access into the application and hence is the most vulnerable area. And typically our application is built with dependencies to a whole bunch of 3rd party libraries and frameworks which inturn depends a whole set of other libraries and so on. This would mean the surface area of the vulnerability is that much bigger and our application is only as secure as the weakest area in the entire codebase.
How about getting rid of authentication logic outside of our application ? In today’s world, there is almost always a ReverseProxy setup in the DMZ(using Apache/Nginx etc.) There are many modules available that handle authentication against LDAP/ActiveDirectory, and to make SAML requests and assertions. Authenticated Requests are forwarded to the application with special headers carrying the Identity Information(username, email id etc.).
The advantage here is that, these libraries are far more visible and are hence far more vetted for vulnerabilities and are actively maintained, when compared to our application code that was handling the authentication logic.
Personally, I have used mod_auth_mellon with Apache and to make SAML integration with SAML based Identity Providers(IdP). This is how my new setup looks like…
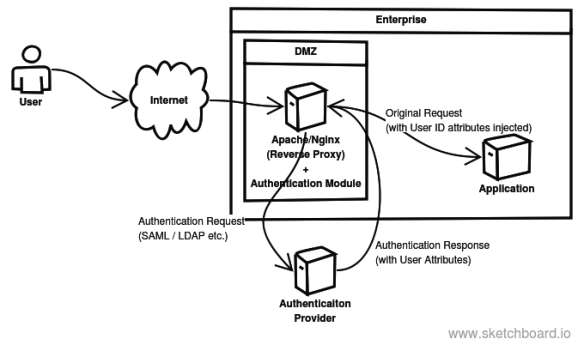
With this above setup, all I will have to check in my application is to ensure the requests are initiated ONLY from a whitelisted IP address and pick up the user context from the special headers passed to it.
